This might be entirely related to Azure AD, but I cannot figure it out.
OIDC works flawlessly while running locally, however once I deploy it Azure throws this error:
AADSTS500117: The reply uri specified in the request isn’t using a secure scheme.
I’ve checked the redirect URL set in Azure AD and its the same one I’m using to access.
Not sure where the problem lies. Any help is appreciated!
Try setting force_https_callback (boom or environment variable)
How can I get a user’s email with OIDC?
It will be available in the flask session in any dash callback.
from flask import session
@callback()
def some_func(*args):
user_email = session["user"]["email"]
# ...
1 Like
I have a question. Generally the basic auth shows up as a pop message while logging in. If I want to design a multi page application with a login page - can I connect the Basic Auth USER NAME and password options to the Password Input and Text input fields of that page?
How are you testing OIDC locally? I am trying to get into this so hoping to learn
@RenaudLN - Does this support multi page apps? I’m trying to integrate into an existing app but I’m not getting redirected to my OIDC provider.
EDIT: I should clarify that I’m running the app in a Docker container and mapping my localhost:8050 to the container 8050. Not sure how this might effect things.
Here’s what I have:
Hey @Mattriggs yes this works with multi-page apps and I’ve been using it in production environment without problem.
Do you get any error logs that could point to what’s going wrong?
Haven’t tried from a local Docker container but it works fine with Docker on the cloud.
Looks like it was from running in the container. I’ve since ran the app locally and had no issues. I won’t be looking further because this shouldn’t be an issue once I have this running in a cloud dev environment.
@RenaudLN How can I get the groups that a user is apart of when using OIDC? It doesn’t seem like that is loaded into any flask session variables. I’m using Microsoft Entra ID as the provider. Does that have to be a separate API request?
This is something you need to define on your IDP so that custom claims (like user groups/roles) are passed to the OIDC token.
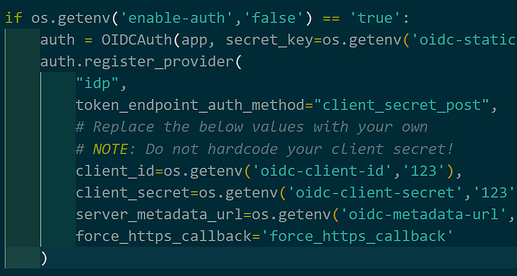
@RenaudLN I’m trying to connect to OIDC provider in Production but https is required. I tried setting the force_https_callback parameter but it’s still creating the redirect URI as http. Am I doing it correctly?
Environment variable is set to true:

Hey @Mattriggs, I think you might need to make the envvar uppercase?
@RenaudLN I tried uppercase but still getting the same error 
force_https_callback is set on OIDCAuth, not on register_provider
it seems like literally amazing
is it possible to manage multiple tenants with the same idp ? should i register a provider for each tenant ?
thx
Yes and yes  you’ll also need to define an idp selection route to handle the various providers
you’ll also need to define an idp selection route to handle the various providers